
Tor Browser13.0.5





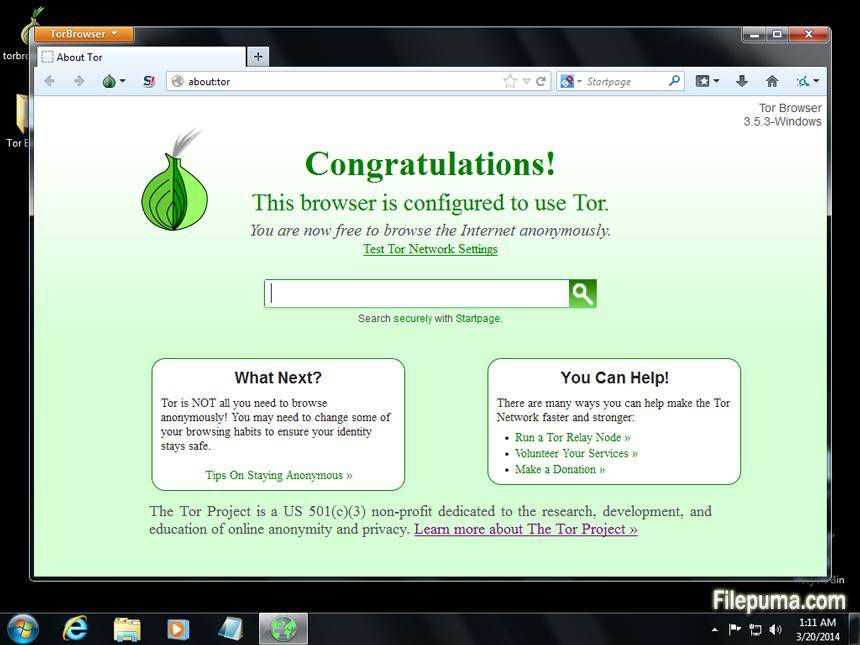
Tor Browser is a free and open-source web browser that provides users with anonymity and privacy while browsing the internet. The browser is based on the Firefox web browser and utilizes the Tor network, which is a system of virtual tunnels that allows users to send and receive data anonymously.
One of the main features of Tor Browser is its ability to hide a user's IP address and location. This is achieved by routing a user's internet traffic through a series of servers around the world, making it extremely difficult for anyone to trace the user's online activity back to their physical location.
Tor Browser also includes additional privacy features such as blocking third-party trackers, disabling browser plugins, and clearing browsing history and cookies upon exiting the browser. This makes it a popular choice for individuals who are concerned about their online privacy and security.
While Tor Browser is primarily used for anonymous browsing, it can also be used to access websites that may be blocked in certain countries or by certain internet service providers. This is because the Tor network allows users to bypass internet censorship and access content that may otherwise be unavailable.
However, it is important to note that using Tor Browser does not make a user completely anonymous online. It is still possible for advanced attackers to identify a user's activity on the internet, especially if the user engages in risky behavior such as downloading files from untrusted sources or logging into personal accounts while using Tor.
Tor Browser is a powerful tool for individuals who value their online privacy and security. Its use of the Tor network provides anonymity and access to otherwise restricted content, but users should still exercise caution when using the internet to ensure their safety and privacy.
Key Features:
- Anonymous browsing through Tor network
- Encryption of data sent between computer and Tor network
- Block third-party cookies and does not save browsing history
- Automatic HTTPS connection when possible
- Built-in security features such as NoScript and security slider
Program available in other languages
- Télécharger Tor Browser
- Herunterladen Tor Browser
- Scaricare Tor Browser
- ダウンロード Tor Browser
- Descargar Tor Browser
- Baixar Tor Browser
User Reviews
User Rating
License:
Free
Requirements:
Windows All
Languages:
Multi-languages
Size:
96.0MB
Publisher:
Updated:
Nov 27, 2023
Clean
Report Software
Latest Version
Old Versions
Developer's Software
Security Levels
To avoid any potential harm to your device and ensure the security of your data and privacy, our team checks every time a new installation file is uploaded to our servers or linked to a remote server and periodically reviews the file to confirm or update its status. Based on this checking, we set the following security levels for any downloadable files.
 Clean
Clean
It is highly likely that this software program is clean.
We scanned files and URLs associated with this software program in more than 60 of the world's leading antivirus services; no possible threats were found. And there is no third-party softwarebundled.
 Warning
Warning
This program is advertising supported and may offer to install third-party programs that are not required. These may include a toolbar, changing your homepage, default search engine, or installing other party programs. These could be false positives, and our users are advised to be careful when installing and using this software.
 Disabled
Disabled
This software is no longer available for download. It is highly likely that this software program is malicious or has security issues or other reasons.
Submit a Report
Thank you!
Your report has been sent.
We will review your request and take appropriate action.
Please note that you will not receive a notification about anyaction taken dueto this report.We apologize for anyinconvenience this may cause.
We appreciate your help in keeping our website clean and safe.

 Free Download
Free Download 

 Tor Browser 15.0.10
Tor Browser 15.0.10 Google Chrome (64bit) 147.0.7727.117
Google Chrome (64bit) 147.0.7727.117 Google Chrome (32bit) 147.0.7727.117
Google Chrome (32bit) 147.0.7727.117 Mozilla Firefox (32bit) 150.0
Mozilla Firefox (32bit) 150.0 Mozilla Firefox (64bit) 150.0
Mozilla Firefox (64bit) 150.0 Maxthon (64bit) 7.5.2.5801
Maxthon (64bit) 7.5.2.5801